 Herein lies the secret. Implementation of a risk management
framework alone is a failure. Governance is mastery of the maturity necessary to
deliver trusted levels of assurance. Delivered with confidence. Cold hard
facts. Where is the quantifiable data? Where are the artifacts? How are they
trending?
Herein lies the secret. Implementation of a risk management
framework alone is a failure. Governance is mastery of the maturity necessary to
deliver trusted levels of assurance. Delivered with confidence. Cold hard
facts. Where is the quantifiable data? Where are the artifacts? How are they
trending?
The number of intersecting information vectors makes it
nearly impossible to deliver security and compliance with any real confidence –
trusted levels of assurance. This is true for any industry, and particularly
true for highly regulated industries that must face the growing diversity of
regulations, standards, and security best practices across internal, external,
and geopolitical pressures. This is complicated further by the duplicity of
compliance requirements without a single governing and centralized source of
information defining the intent or expected implementation across all
technologies. This is the elephant in the room. This is the situation. The
complexity lies in the ever-growing legal jargon of requirements and the
exponential growth in new market-disrupting capabilities driven by new
technologies and new platforms. The underlying question is whether what you’re
doing now is meeting the bare necessity, the status quo, or do you have an
opportunity to change the game.
Providers and Consumers
Managing sensitive data is a significant challenge as the
number of factors providing inputs into the operational processes and the
number of recipients consuming the outputs of the operational processes
continue to increase. This is true of all information that is stored,
processed, and transmitted across your infrastructure. The additional challenge
in this regard is from vendors provided sensitive access to your systems and
the growing rights of consumers over their own information. This affects
business relationships, consumer relationships, and puts a square demand on the
organization to demonstrate to both that they can protect their data.
Cost of Compliance
The cost of compliance continues to escalate for obvious –
and not so obvious reasons. The obvious reason is that we must deal with an
increasing number of regulations and standards that affect our business,
particularly in highly regulated industries and geopolitically affected
organizations. However, there is more.
There is a disconnect between the steps necessary to build a
secure (compliant) system (and architecture) and the steps necessary to sustain
compliant systems. The first one involves building a system securely at a
point state in time. The second one involves understanding that state
changes over time and governing factors such as patch management, configuration
management, architecture reviews, policy reviews, and several other factors
affect the ongoing security and compliance of that same system.
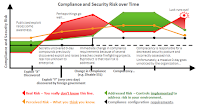
In simple terms, this is a governance problem. This leads to
dangerous situations in which you have a perceived risk (what you think you
know) that is less than your real risk (what you don’t know) because you don’t
have the complete story or it’s not properly understood and calculated in
context. Much could be written about both, but these are self-explanatory. You
either view and calculate risk in context – addressing out-of-bounds conditions
– or you suffer the consequences.
Tools are bought to address this problem. However, tools are
unfortunately often poorly utilized, and poorly understood. The financial
services sector has been noted by several studies as having the most tools of
any industry vertical. This means that financial services have more panes of
glass, and possibly more information and input to identify issues and problems.
The reality is that unless you have a system for prioritizing the impact in
both a general and very specific sense, you will never be able to address the
issues that eventually lead to an infrastructure breach.
Related to this is the reactive phenomenon of external
audits. It’s quite interesting, like tax season, everyone seems caught off
guard during an external audit. Why is an external audit a surprise? Why is it
so often a forcing function? The situation would change completely given a
system that is designed to manage and store for future retrieval the essential
artifacts requested during an audit. This takes the burden off system operators
from running around checking their systems and shifts their focus to driving
the day-to-day activities they are hired and trained to perform.
Cost of Security
As the tired story of growing threats continues to get the
headlines, the perpetrator for many of the successful penetrations is related
to the increasingly agile business. Organizations are turning new features and
technologies out faster than they can effectively review them to create a
market edge. This is challenging because you need to innovate and respond to
the market with new features and capabilities to create parity with, or
dominate, your competition. However, as an attacker, I just need one mistake.
The situation for security is that we have a complex and
dynamic IT infrastructure extended across locations, acquisitions, technology
platforms, and decades of technical debt.
The complexity here is compounded tremendously when you
consider the challenges of creating “cloud-native” applications alongside
existing mainframe technologies. Cloud-native is a moniker that can include
containers or any other technology that allows elasticity and other advantages
of cloud technologies. Many of these are still tightly interconnected. The
challenge to change is equally met by the challenge to secure. The question
then becomes, “How can I dynamically manage technology risk?”